Mandatory Access Control for High-Security Sites With Acre
.webp)
In most organizations, an access error is an inconvenience. Someone gets into a floor they should not have accessed, an audit flag appears, and an administrator corrects the permission. In high-security environments, the calculus is entirely different.
A government estate where classified data and operational systems share a building cannot tolerate permission gaps. A critical infrastructure site where a single unauthorized access to a control system could cascade into a service failure cannot rely on administrators catching errors after the fact. A healthcare facility handling highly sensitive patient records cannot grant access based on job title alone and hope for the best.
These environments need mandatory access control: a centrally managed, classification-based access model where security labels and clearance levels govern every access decision, and no user or department can override those rules. The system enforces policy. There are no exceptions and no workarounds.
Note: Acre's access control platform is designed to support mandatory access control requirements across regulated, high-security, and air-gapped environments. Talk to the Acre team to discuss your site requirements.
Why Standard Access Control Models Are Not Enough for High-Security Sites
Role-based access control and discretionary access control work well for most enterprise environments. For environments where security is the primary constraint, that flexibility is also their weakness.
In a discretionary access control model, resource owners can share their own access rights at their discretion. That means sensitive areas can be made accessible without centralized oversight, often through informal decisions that bypass formal security policies. For organizations handling classified data or operating under strict regulatory requirements, that exposure is unacceptable.
Role-based access control improves on this by centralizing permission management around organizational roles, but it still falls short when access decisions need to account for security classifications. A role grants access to a category of resources. It does not distinguish between resources of different sensitivity levels within that category, and it offers no mechanism for enforcing clearance-based restrictions automatically.
Mandatory access control removes the ambiguity. Access permissions are determined by the clearance level of the user and the security classification of the resource. The central authority sets and enforces the policy. Users, departments, and resource owners have no ability to modify access rights or create exceptions.
If you're evaluating a high-security access control system, understanding the long-term cost is just as important as the security model.Try Acre’s total ownership cost calculator to estimate the total cost of ownership and see how modern access control platforms compare over time.
How Acre Supports Mandatory Access Control Across Your Environment
Acre's access control portfolio is built to serve organizations at both ends of the security spectrum: cloud-native deployment for distributed enterprise environments, and fully on-premises, air-gapped deployment for sites where network isolation is a security requirement. Both models support the centralized policy enforcement, security labeling, and detailed audit trails that mandatory access control demands.
ACTpro for Air-Gapped and Sovereign Sites
For government estates, defense sites, and regulated facilities that require local, sovereign control with no dependency on external networks, Acre's ACTpro is the on-premises access control platform designed for exactly this profile. It runs on a central server with door controllers managing physical access, and it supports wired and Aperio wireless lock integration across large door counts.
ACTpro is proven in government and heritage environments where network isolation is a requirement and where the access control system must operate independently of cloud infrastructure. Clearance-based access policies are managed centrally by system administrators, and changes are enforced in real time across every connected door and reader on site.
Read more: 11 Features to Consider when Selecting the Right Access Control Solution
Acre Access Control for Enterprise-Scale Enforcement
For organizations requiring MAC-style controls across distributed sites without the constraint of air-gapped operation, Acre's cloud-native access control platform provides centralized policy management from any device, with changes applied in real time across every location. Security teams can define classification-based access permissions, configure role and clearance hierarchies, and enforce system-wide lockdowns instantly.
The platform supports biometric credentials and mobile, multi-site administration, and integration with identity and HR systems, enabling automated updates to clearance levels and access permissions when organizational data changes.
Hybrid Deployment for Mixed-Security Estates
Many high-security organizations operate mixed estates: air-gapped on-premises access control for sovereign or classified areas, alongside cloud-based visitor management and workflow tools for the parts of the estate that do not require network isolation. Acre's hybrid deployment model supports exactly this pattern.
A government estate, for example, can run ACTpro fully on-premises for core access control while using Acre's Enterprise Visitor Management in the cloud for reception workflows, pre-registration, and auditable visitor logs. The result is sovereignty where the security policy requires it, and operational efficiency everywhere else.
Acre has delivered hybrid deployments across government, critical infrastructure, and enterprise environments. Talk to the Acre team to discuss the right architecture for your site.
Where Mandatory Access Control Delivers the Most Value
Mandatory access control is not a universal solution. It is the right model for environments where the cost of unauthorized access is high, where regulatory requirements specify centralized enforcement, and where user discretion over access rights cannot be tolerated. Acre supports MAC requirements across the following sectors.
Government and Defense
Government and defense environments handle classified data and critical operations that require strict separation of access by security level. Mandatory access control enforces this through security labels applied to both users and resources: Top Secret, Secret, Confidential. Access is granted only when a user's clearance level matches the resource's classification, with no temporary overrides available to local teams.
Acre's ACTpro platform supports this model on-premises, with centralized administration and detailed access logs recording every granted and denied access attempt. The hybrid deployment pattern adds cloud visitor management for multi-site government estates while keeping access control sovereign and air-gapped.
Critical Infrastructure
Power plants, water treatment facilities, and transport hubs use mandatory access control to restrict physical access to control systems and operational areas. An unauthorized access attempt in these environments is not a compliance issue to be resolved after the fact. It is a potential operational incident.
Acre's access control system supports multilevel security configurations that restrict access to high-security areas based on clearance level, with real-time alerts and automated responses when access is denied or rules are violated. System-wide lockdowns can be triggered instantly from a central interface, without requiring administrators to be on-site.
Healthcare: Separating Sensitive Records by Clearance
Healthcare organizations operating under HIPAA and similar regulatory requirements need to demonstrate that highly sensitive patient data, such as psychiatric records, oncology records, or infectious disease information, is accessible only to personnel with documented clearance to handle it. Role-based access control is often insufficient for this requirement because it grants access to a category of records rather than distinguishing between sensitivity levels within that category.
MAC addresses this through security classifications applied to data and physical areas alike. Only personnel whose clearance level meets the classification can gain access. Acre's platform records every access attempt, granted or denied, providing the audit trail that compliance frameworks require. Learn more about access contro
How Mandatory Access Control works
MAC works by enforcing access policies based on three core elements:
- Security labels are applied to users and resources.
- Clearance levels determine what users are allowed to access.
- System-level enforcement means rules cannot be bypassed by local teams or individual resource owners.
Access decisions are binary. Either the user’s clearance meets the resource’s classification or it doesn’t. There is no room for exceptions or temporary overrides.
A quick example
A defense contractor configures access so that only users with Level 4 clearance can enter R&D areas handling export-controlled technology. Even if a user has a mobile credential and badge access, the system denies entry unless their clearance level matches. Security teams manage this centrally and can update classifications in real time across all locations.
Mandatory Access Control vs Other Access Control Models
Understanding where mandatory access control fits relative to other models is important for organizations evaluating access control options or combining multiple models. The table below compares MAC against role-based access control (RBAC), discretionary access control (DAC), and rule-based access control (RuBAC).
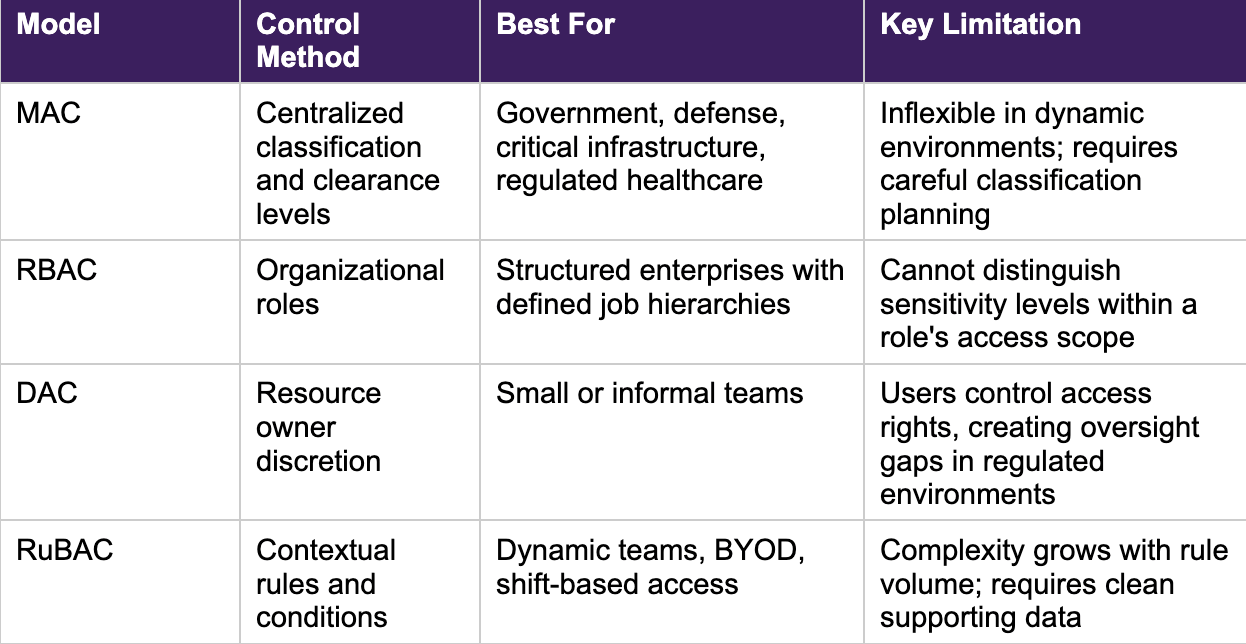
Many high-security organizations combine MAC with RBAC or rule-based access control: MAC enforces clearance-based restrictions on the most sensitive areas, while RBAC or RuBAC manages access across the broader environment. Acre's portfolio supports this layered approach, with on-premises and cloud deployment options that can be configured to enforce different access control policies at different security levels within the same estate.
Implementing Mandatory Access Control: Challenges and How Acre Addresses Them
Implementing mandatory access control is more demanding than deploying role-based or discretionary models. It requires a clear classification system, centralized administrative oversight, and an access control platform capable of enforcing policy without relying on individual users or departments to manage their own access rights. These challenges are real, but they are manageable with the right planning and the right platform.
Read more: 7 Benefits of Implementing an Access Control System in Your Security System
Maintaining Classifications as Organizations Change
Mandatory access control systems require continuous administrative oversight. When staff change roles, when new resources are added, or when security requirements change, the classification system needs to be updated to reflect those changes. In large organizations, the volume of updates required can become a significant administrative burden.
Acre's platform integrates with HR and identity systems, automating updates to user clearance levels and access permissions when organizational data changes. This reduces the manual workload on security teams and limits the risk of stale permissions accumulating across the system.
Testing Before Deployment
A misconfigured security label or clearance level can either lock legitimate users out or fail to block access that should be denied. Acre recommends starting with a defined pilot set of high-priority access points, testing against real access scenarios, and resolving conflicts before rolling out across the full estate. Talk to the Acre team to plan a pilot for your environment.
Why High-Security Organizations Choose Acre for Mandatory Access Control
Acre is trusted by organizations including Dublin Airport Authority, Google, Pinterest, and The Ritz London. Our access control portfolio spans cloud-native, on-premises, and hybrid deployment models, giving high-security organizations the flexibility to choose the architecture that matches their security requirements without compromising on functionality.
What Acre brings to mandatory access control deployments:
- On-premises, air-gapped deployment via ACTpro for sovereign and classified environments
- Cloud-native centralized access management for distributed enterprise sites
- Hybrid deployment: on-premises access control alongside cloud visitor management
- Centralized security policy management with real-time enforcement across all connected doors
- Full audit trails for every access attempt, granted or denied
- Real-time alerts and automated responses to access violations
- System-wide lockdown capability, triggerable from any device
- HR and identity platform integration for automated clearance level management
- Multilevel security configurations across mixed-classification estates
ISO 27001 certification applies to specific parts of Acre's portfolio. SOC 2 applies to cloud access control. Verify scope for your deployment. Talk to the Acre team to discuss your compliance requirements.
Protecting High-Security Environments with Acre
Mandatory access control is the right model when the cost of an access error is too high to accept. If your organization operates in a regulated, classified, or critical infrastructure environment, the access control system you deploy needs to enforce policy without exception and document every access decision with a complete audit trail.
Acre gives high-security organizations the tools to implement and maintain mandatory access control across on-premises, cloud, and hybrid environments.
Why organizations use Acre security for high-security access control
Acre helps organizations enforce MAC-style controls without compromising operational performance. Whether you’re in defense, manufacturing, energy, or healthcare, Acre gives your team the tools to define, manage, and enforce the strictest access policies from a single platform.
Key advantages:
- Centralized policy control from any device
- Real-time access updates synced with HR and IT systems
- Mobile credentials, QR check-ins, and zone-based enforcement
- Granular access logging and audit trails
- Support for security labels and clearance-based workflows
- Multi-site visibility with local autonomy
Acre is trusted by organizations that cannot afford access errors. We help security teams lockdown sensitive environments while staying agile
Need to protect what matters most?
Talk to Acre about high-security access solutions built for your risk profile.
Is MAC right for your organization?
Mandatory Access Control is a strong choice when:
- You deal with sensitive or classified information
- You need to meet compliance requirements that demand tight access boundaries
- You want full control over who gets access, with no exceptions
MAC is not for every organization. It requires planning, classification structures, and a centralized approach to security governance. But when the cost of compromise is high, MAC is the right tool for the job.
If you're unsure how to implement MAC or integrate it with your current systems, talk to our team at Acre. We’ll help you assess your access control needs and design a system that protects your most critical assets without slowing you down.
Frequently Asked Questions: Mandatory Access Control
What is meant by mandatory access control?
Mandatory access control (MAC) is an access control model where a central authority enforces access policies based on security classifications. Users are assigned clearance levels and resources are assigned security labels. Access is granted only when a user's clearance meets the resource's classification. Neither users nor resource owners can modify these rules.
What is the main difference between DAC and MAC?
In discretionary access control (DAC), resource owners control who can access their own resources and can grant or revoke access at their discretion. In mandatory access control (MAC), a central authority enforces access permissions based on predefined security policies and classification levels. Users in a MAC system have no ability to modify access rights. This makes MAC significantly more secure but less flexible than DAC.
What is an example of mandatory access control?
A defense contractor configures access so that only users with a Top Secret clearance level can enter the R&D area handling export-controlled technology. Even if a user holds a valid credential and has physical access to the building, the MAC system denies entry unless their assigned clearance level matches the security label on that area. Security teams manage all classifications centrally and can update them in real time across every site.
What are the four main types of access control?
The four primary access control models are mandatory access control (MAC), role-based access control (RBAC), discretionary access control (DAC), and rule-based access control (RuBAC). MAC is the most restrictive, using centralized classification to govern access. RBAC assigns permissions by organizational role. DAC gives resource owners control over their own resources. RuBAC adds conditional logic based on time, location, or device context.
Can mandatory access control be combined with other models?
Yes. Many high-security organizations layer MAC with RBAC or rule-based access control. MAC handles the most sensitive areas using clearance-based restrictions, while RBAC or RuBAC manages broader access across the rest of the estate. Acre's platform supports this combined approach across both on-premises and cloud deployments.



